FAQ - Usage of the IP Protector
this tool is no longer in use, contact support@digistamp.com
A directory of FAQ's on other timestamp subjects is here.
A new alternative to the IP Protector are our web applications available here.
Click here for resolutions to installation problems.
Click here for alternative web-based applications.
When the software detects a software error, it records that error in a file to help us diagnose the problem. The name of the error log file is IPPROT.LOG and is stored in the installation directory.
Start the IP Protector application and use this technique to create an e-mail to send to support.
Or, to find the installation directory where this file is stored on your computer click here.
You should regularly backup the files below to another location (e.g. CD or floppy disk). It is crucial that the documents that you have time stamped also be preserved without changing their contents.
You have the option of exporting a copy of the individual timestamps and the protected content to a file on your computer. To use export, start the IP-Protector software and click the "Export" button on the main window. This is described here.
Your time stamp certificates are stored on your computer in these two files:
- IPPDB3.odb
- IPPDB3.odt
To find the directory where these files are stored on your computer click here. This window also allows you to specify the directory used.
The directory name will be "eTime". For example, on my computer it is stored at "C:\Documents and Settings\Chris\eTime"
The problem you are seeing is related to the connection to the Internet. You need to diagnose why the Java/IP Protector program is not able to access the Internet. Ideas:
- Is your account number entered correctly, make sure no spaces. Go to the 4th tab "billing" and retype your account number with no spaces at the end. Then try again.
- Disable the use of SSL. Go to the 3rd tab "options" and un-select the "Use an SSL connection". Close and restart the IP Protector and then try again.
- Do you have local, Personal firewall software like Zonealarm or some versions of Norton prevent programs from accessing the Internet? You may need to configure local firewall software to allow the DigiStamp software to access the Internet. (The Windows firewall should not be causing this problem). Please disable or turn-off the outgoing firewall and perform the same test? Technically, you want to allow the Java program to communicate out to the Internet on ports 80 and 443.
- Establish and test your Internet connection is working before starting the IP Protector software. Exit and restart the IP Protector software.
Symptom, what the software says when trying to create a time stamp:
- Calculating Hash value for xxxx
- Transmitting request to (SSL) TSA1
- Communications failure will retry 1 more times Transmitting request to (SSL) TSA2
- Communications failure Failed Internet communications
For example, you may want to store your data on a central network storage device. There are two approaches. We suggest that you use the "export" method below.
"Export" the time stamp and your data immediately after they are created. This is described here. Using this method you would then have two copies, one copy in your local environment and the exported copies. We suggest not using the "zip" option for this purpose of creating backups as it makes your data a little more difficult to manage. This method is convenient because you can readily identify the file names of the documents and their time stamps in the export target directory. This method is more reliable because it separates your data from the use of IP Protector. That is, the two files created in an export, e.g. "myData.doc" and "myData.doc.p7s", and stored in a way that any software that understands signature/time stamps can view the data - you are not dependant upon the IP Protector software.
Another alternative is to configure IP Protector to save its databases in an alternate location. The configuration option is show here . This option is not available unless you have created at least one time stamp. This is an advanced option and you should not use this unless you are comfortable with manually moving files on your computer. Also, moving the database files to a "network drive" can cause problems if that network drive is not always available when you run IP Protector. We suggest that you use the "export" method above.
. This option is not available unless you have created at least one time stamp. This is an advanced option and you should not use this unless you are comfortable with manually moving files on your computer. Also, moving the database files to a "network drive" can cause problems if that network drive is not always available when you run IP Protector. We suggest that you use the "export" method above.
BACKGROUND: A time stamp is verified using a public key certificates. A single public/private key-pair will be used to create many timestamps at the DigiStamp server.
To resolve:
- Display a time stamp that has not verified in the right side of the "manage" tab.
- Click the printer icon / button in the upper right. Scroll down in the print preview window to the field labeled "Public key serial number".
- The serial number is part of the name of the certificate file. For example for serial number 46, then you need to import the DigiStamp certificate in the file DGS46.CER. Download that particular serial number certificate from here.
- Go to the third tab, called "user preferences". Use the import button at the bottom left to "import" the certificate into the section labeled "Trusted for this Application".
After the import you will need to close and reopen the IPP software to force it to revalidate using the newly imported certificate. Also, there is information here that demonstrates the relationship within the IPP software; see the two camera / screen prints.
Internet or Cloud storage evolution may be changing best practices for long term storage, minimally adding easy opportunities for multiple copies. A prior technology method that has common acceptance is coping your data to "write once" type media like CD-ROM or DVD for storage periods of 1 or more years. Best to have two seperate copies of the files on the media and more than one copy of the media. Time stamps are sensitive to any data change.
Long term archiving of digital data is a challenging task. Especially when preserving the data for 10, 50 or more years. There are many opinions on this subject and the solution to your particular situation may vary. Long term archiving of digital data is a subject of research for several government and independent organizations. We provide some references at the end of this section.
Below we provide some suggestions and ideas for preserving your digital data.
Media decay - Storage of the media is a key factor. Consider controlling temperature, exposure to sunlight and pollution. Tape and diskette are the most susceptible to the effects of the environment and some opinions state that these mediums are reliable only for about 3 years. Manufacturers of CD-ROMs sometimes claim their product is reliable for a hundred years or more. The newer CD-ROM’s are more reliable; 25 years seems a reasonable estimate. But the industry does not have sufficient experience to truly know how long a CD-ROM will last. CD-R is probably a better choice as compared to CD-W. Always choose high quality products. Some opinions are the DAT or DLT are a good choice.
Another practical approach to minimize the risk of media decay is storing several copies of your digital data. That would be, for example, writing the data to two different CD-ROM’s or minimally writing the data twice to the same CD-ROM.
Hardware obsolescence – This is the situation where the media you have recorded is not supported by current hardware. We suggest a media like CD-ROMs will be available for many years to come.
A solution to media decay and hardware obsolescence can be a practice of “migrating to new storage” by moving you data to newer mediums over time. This would be for example, copying you diskettes to CD-ROM today. Later, copying the CD-ROMs to whatever is a predominant media in 5-10 year horizon.
Software obsolescence – This is the situation where the software used to create your digital data is no longer available at some future point. It is unclear how significant of a risk this poses. For example, there are common formats today that are used heavily with millions of dollars invested in government and independent archives. There is good reason to think that common formats like – PDF, TIFF, Jpeg, MS Word, and others – will be, at a minimum, readable for a long period of time. One practical suggest is to not “compress” the data before writing to your storage media to remove the compression as a factor.
As reference:
- U.S. Library of Congress Services of the Preservation Research and Testing Division and here
- An article by Jeff Rothenburg and Copublished by the Council on Library and Information Resources and the Library of Congress
The software will query the DigiStamp servers for upgrades each time you start the software (if you were connected to the Internet). If you would like to check for manual updates (not recommended) then those are located here.
You may choose to completely uninstall the software from a computer. Or, you may want to uninstall and reinstall to refresh your copy of the software.
Instructions to launch Java Application Manager "Cache Viewer"
- Go to Start > Control Panel > Double click on the Java icon. The Java Control Panel will start.If you have problems finding Java in the "Control Panel"; you are looking for "Java" and you may need adjust the view to "Small icons" or click on the "Program" icon to show the details of the Control Panel.
- Click on the General tab
- Click on the View... button
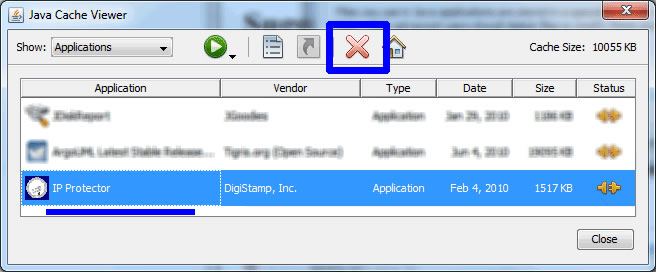
- Select Show Applications
- Right-click on the IP Protector application from the list that you want to launch, delete, create shortcuts
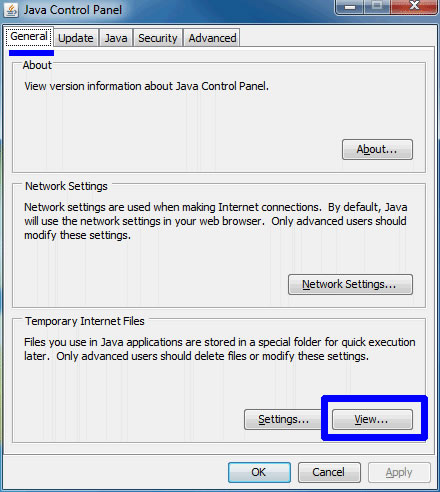
Uninstall by clicking the large, red, X.
Alternative ways to open Java Application Cache viewer:
Windows
- Click on the "Start" icon in the lower left hand corner of your screen, followed by clicking on the "Run" menu choice.
- In the run box, type "javaws -viewer" (w/o the quotes) and hit "Enter"
Linux
- type in the command "$JAVA_HOME/jre/javaws/javaws" on the command line.
- the application you need to clear your cache will then display itself as "Java Application Cache Viewer"
Mac OS X
- Open a Finder window,
- Choose "Applications", "Utilities", "Java" and open Java Web Start,
- Click the Java Web Start menu and choose "Preferences",
- Click the “Clear Folder” button. Then OK.
Re-install the IP Protector software?
After you complete the previous step of 'clearing the Java Cache', you can reinstall the software and access your data again here.
More Details:
There are three groups of data that comprise the software: 1. Your data that has been created by the software (e.g. your time stamps). 2. The IP Protector software (in the Java Cache) 3. The Java environment itself.
If you are curious about where the Java Cache is stored on your computer click here.
If you want to want to uninstall both IP Protection and the Java environment. Use the add/remove programs function in the Start > Control Panel. You will uninstall the program titled: "Java Runtime Environment".
The files that contain your data (the time stamp and signatures) can be deleted manually. You can backup your data before proceeding with the uninstall process. The directory that contains this data is named "eTime". The directory's location is described here.
To create or a shortcut use the Java Cache Viewer. Once started, highlight 'IP Protector', right click and select 'Install Shortcuts'.
Alternatively, you can create a shortcut by using the link on our installation web page. Shown here: 
Using that web page link that is used to start the IP Protector software, you can right click and choose "save link as", or "save target as". Save this link to your desktop. Then, you can double-click on that desktop shortcut to start the IP Protector software.
An existing shortcut can cease to work if, for example, you update the Java software on your computer. In this case you will need to recreate (delete and then create) the shortcut as described above.