SecureTime® Server
DigiStamp's servers are also available for purchase. DigiStamp began in 1998 as an Internet-based timestamp service. Using our client software and an Internet connection, customers could request a timestamp from one of our SecureTime Servers. This specialized hardware is also available for purchase and operation on your organization's network.
Qualities:
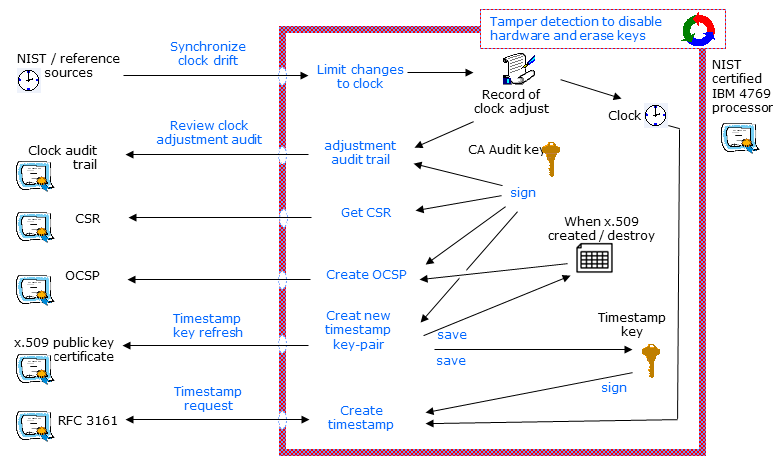
- The RFC 3161 timestamp function is code running within the FIPS 140-2 Level 4 tamper responding certified hardware (HSM). Competing products use the HSM only for the signing function.
- The trust of a timestamp is unique because both the keys and clock must be secured. The HSM's internal clock will not accept adjustments beyond these few, small calibration events per day. Clock value in the HSM persists after the Audit event, across reboots or storage of the HSM. Competitor products do not secure the clock; the clock is external and implies the trust of your organization's administrative process.
- Signing keys are created inside the certified hardware and cannot be exported as internally signed x.509 certificates. OCSP are the same, created within the HSM.
A question: do you need in-house hardware or could you use our Internet or cloud based service?
Table of Contents:
- Who uses the SecureTime Server.
- The security design for the trust model.
- A reliable and scalable solution.
- The valuable support from DigiStamp.
- The server includes tools for integrating timestamps within your organization.
- The pricing options to fit your needs.
There are two types of customers that benefit from the new hardware option:
-
High-volume customers that need dedicated capacity for their internal requests for timestamps. When our customer routinely uses about one per second, then the in-house SecureTime Server can become a cost-effective alternative to DigiStamp's Internet-based solution.
-
Organizations or government agencies that want to establish themselves as a timestamp authority. In this situation, our customer wants to establish a regional timestamp authority that has local customer support and a regional focus to the timestamp service. DigiStamp provides all the software, hardware and processes to quickly establish this new timestamp authority with a distributor agreement and a defined region.
DigiStamp began in 1998 as an Internet-based timestamp service. Using our client software and an Internet connection, customers could request a timestamp from one of our SecureTime Servers. Recently, customers have requested that we provide the option of the customer hosting the SecureTime Server.
The DigiStamp service (hardware, software, and processes) has proven itself by providing reliable service for the past 10 years to thousands of customers, creating millions of timestamps.
SECURITY FOR THE TRUST MODEL
The SecureTime Server comes with the hardware-based security that a timestamp authority demands. The same lock down and audit procedure has been performed on this device as described here:
-
A hardware security module (HSM), which is NIST certified, stores the private key, clock and performs the crypto-functions. The tamper-detection mechanisms destroy the private key if attempts are made to discover the key. Read more about the IBM 4769 Cryptographic Coprocessor here.
-
The HSM is preconfigured by DigiStamp to provide timestamps. All other interfaces have been disabled. The timestamps are implemented as specified by the IETF PKIX TimeStamp Protocol (RFC 3161 and update RFC 5816 for ESSCertIDv2). The signatures use RSA 2048 and 4096 bit key length or ECC 256 and 512 bit key length
-
The clock is inside the HSM and has been set and cannot be adjusted beyond minor updates for clock drift. A software process synchronizes with recognized sources, and DigiStamp remotely audits the clock drift adjustments.
-
The private signing key is initialized inside the HSM in a "no export" manner so that neither you nor DigiStamp can ever see the private key. The private key and clock are bound together in the HSM when initialized.
RELIABLE and SCALABLE
There are three approaches to increasing capacity and managing system or communication outages:
-
The DigiStamp Internet-based service can be a backup to your operations. For example, given an Internet outage at your facility, clients could automatically begin using the DigiStamp set of server locations.
-
Install multiple, independent SecureTime Servers – potentially separate locations. The client toolkits from DigiStamp include the failover logic if a location is unavailable.
-
A cluster of multiple servers is installed using a model for failover and a round-robin load delegation.
SUPPORT for DIGISTAMP
-
Customers can begin by using our Internet-based timestamp service with our API toolkits and desktop application. When their business use grows, they can install the SecureTime Server in-house and centrally configure their current users' software to access the new server.
-
SecureTime Server includes a web-based configuration and monitoring interface. The server has alerts for your operation's support team if internal errors were to occur.
-
Support and Maintenance includes diagnostics, battery replacements and assistance.
TOOL for integration
Customers purchasing the SecureTime Server can also distribute the SecureTime API toolkits. Distribution rights will be limited to within the corporation that purchased the SecureTime Server.
PRICING options
HSM with the Application server software installed and configured with hosting hardware.(1)
Contact us for a quote.
Support and annual maintenance fee. First year is included.(2)
$6,000/year
Licensed copies of SecureTime API toolkit for Java
No charge
(optional) DigiStamp failover access priced based on capacity. This would be a feature for your disaster recovery plans. One-time setup fee $1,000.
Annual fee of $2,000 per capacity increment of 1 transaction per second. Actual failover events are charged at the regular pricing plan starting at $.26.
(optional) Support upgrade to include a guarantee for next day shipment of replacement.
$5,000/year
(1) A 2U, rack-mounted IBM System x Server. Optional hardware choices are available based on customer specifications.
(2) Installation requires an outbound Internet connection for clock synchronization events. Extended Support can be purchased within 90 days of original equipment purchase.
The SecureTime server and the DigiStamp software that it contains is licensed for use within a single organization and does not include distribution rights to the general public, for reselling the timestamp service or for reselling the device.
A one-year limited warranty on hardware purchased from DigiStamp. The HSM has handling, operational and environmental requirments related to tamper detection mechanisms. The warranty does not include if a tamper event is detected by the HSM. DigiStamp can supply used hardware that has been used for extended tests or within DigiStamp operations.